
IMO Cyber Risk Management Explained for Fleet Operators
Why maritime cyber risk governance is now core to safe, compliant and resilient shipping
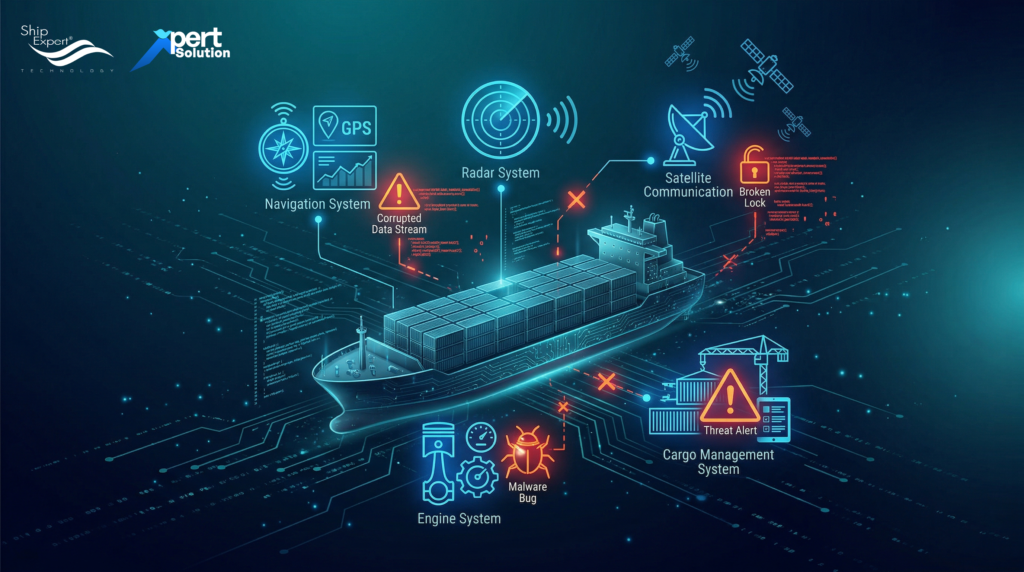
In today’s maritime landscape, digital technologies are everywhere — from navigation and communication systems to cargo management and engine monitoring. But with increased connectivity comes increased vulnerability to cyber threats that can disrupt vessel operations, compromise safety, or even lead to regulatory non-compliance. This is why cyber risk management has become a central governance topic for fleet operators worldwide.
In response to these threats, the International Maritime Organization (IMO) has developed formal guidance requiring ship operators to integrate cyber risk management into their safety frameworks — a change that is reshaping how fleets are governed and audited.
Why Maritime Cyber Risk Matters
Unlike traditional IT systems, vessel systems are often deeply integrated with critical operational technology (OT) — such as propulsion control, cargo systems, and navigation networks — meaning a cyber incident can directly affect the physical safe operation of a vessel. These systems are essential for safe and efficient ship operations, yet they also present attractive targets for attackers if not properly secured.
Many maritime cyber incidents begin with seemingly minor vulnerabilities, such as unprotected network access, out-of-date software, or unsecured remote connections. Left unmanaged, these vulnerabilities can cascade into operational failures, safety breaches, or downtime that impacts schedules, profitability, and reputation. Effective risk governance is therefore no longer optional — it’s required.
IMO’s Response: A Governance Framework
In recognition of the growing cyber threat landscape, the IMO adopted Resolution MSC.428(98) in 2017, which encourages administrations and operators to address cyber risks within their Safety Management Systems (SMS) aligning cyber risk management with the well-established International Safety Management (ISM) Code.
Following this, the IMO issued Guidelines on Maritime Cyber Risk Management (MSC-FAL.1/Circ.3 and subsequent revisions), providing high-level recommendations on how organizations should manage cyber risks in a systematic and integrated way. These guidelines are intended to be incorporated into existing risk management processes and complement traditional safety and security practices.
Core Functional Elements of Cyber Risk Management
The IMO guidelines define several key functional elements that should form the backbone of a maritime cyber risk governance program:
1. Identify
Identify all vessel systems, assets, data, and interfaces that could be impacted by cyber threats and maintain a current inventory of these systems. Understanding what you have is the first step in knowing what you need to protect.
2. Protect
Implement protective measures — both technical and organizational — to minimise the likelihood of cyber incidents. This includes network segmentation, access control, patch management, and secure configuration practices.
3. Detect
Maintain ongoing monitoring and detection capabilities to identify suspicious activities or breaches early. Rapid detection reduces the impact of cyber events and enables timely response.
4. Respond
Develop clear procedures for responding to cyber incidents, including roles, communication plans, and escalation paths, both onboard and with shore-side support teams.
5. Recover
Establish recovery strategies to restore systems and operations after a cyber incident, ensuring continuity and minimal operational disruption.
These functional elements closely align with internationally recognised cybersecurity frameworks, such as ISO/IEC 27001 and the NIST Cybersecurity Framework, providing a structured approach that can evolve with emerging threats.

Integration With the ISM Code
The IMO’s Resolution MSC.428(98) explicitly encourages cyber risk management to be integrated into the Safety Management System (SMS), which means operators must treat cyber risk like any other safety risk — assess it, manage it, and demonstrate evidence of that process during ISM audits.
Common Gaps in Maritime Cyber Governance
Despite this guidance, many fleets still struggle with implementation. Risk assessments may be incomplete, documentation may be outdated, and crew awareness of cyber threats can be minimal. Often, there is no centralized visibility of cyber activities or incident response planning, leaving vessels exposed to avoidable risk.
For a robust governance posture, maritime operators should:
- Conduct regular cyber risk assessments
- Document policies and procedures clearly
- Assign accountability for cyber governance
- Train crew and shore staff on cyber hygiene
- Implement monitoring and incident response capabilities
This structured approach ensures compliance with IMO guidelines and strengthens operational resilience against cyber events.

Why Centralized Maritime SOC Matters
Modern vessels operate as cyber-physical systems, integrating:
- Navigation systems (ECDIS, Radar, GNSS)
- Satellite communication networks
- Engine and propulsion monitoring systems
- Cargo management platforms
- Crew internet and remote vendor access
Without centralized monitoring, cyber incidents may go undetected until operational disruption occurs.

A maritime-focused Security Operations Center (SOC) enables:
- Real-time anomaly detection
- Centralized log monitoring
- Shore-based cyber oversight
- Coordinated incident response
- Compliance-ready reporting for audit purposes
Continuous monitoring transforms cyber management from reactive troubleshooting into structured governance.

Introducing V.Secure – Maritime Cyber Governance Support
V.Secure is maritime cybersecurity and SOC framework, designed to align with IMO cyber risk management principles.
Rather than replacing internal policies, V.Secure strengthens implementation through:
- Centralized maritime SOC monitoring
• OT-aware anomaly detection
• Fleet-wide cyber visibility
• Incident coordination support
• Governance-level reporting
By integrating monitoring, detection, and response capabilities into fleet operations, V.Secure helps operators operationalize the IMO framework — not just document it.
In practical terms, this means:
- Compliance officers gain structured reporting
- Fleet managers gain operational visibility
- Technical teams gain faster incident response capability
Cyber governance becomes measurable, auditable, and defensible.

Conclusion
IMO Cyber Risk Management is not merely regulatory guidance — it is a strategic framework for managing operational exposure in modern shipping.
By integrating policy, process, technical safeguards, and centralized monitoring, fleet operators can transform cyber risk from vulnerability into a governed operational domain.
In an industry where safety, reliability, and reputation are critical, cyber governance is no longer optional.
It is infrastructure.

References
-https://wwwcdn.imo.org/localresources/en/OurWork/Security/Documents/MSC-FAL.1-Circ.3-Rev.3.pdf?
– https://www.imo.org/en/ourwork/security/pages/cyber-security.aspx?
– https://www.dnv.com/maritime/insights/topics/maritime-cybersecurity/regulations/?
– https://www.imca-int.com/resources/technical-library/imo-guidelines-on-maritime-cyber-risk-management/?
– https://gtmaritime.com/imo-the-ism-code-and-maritime-cyber-risk-management/?